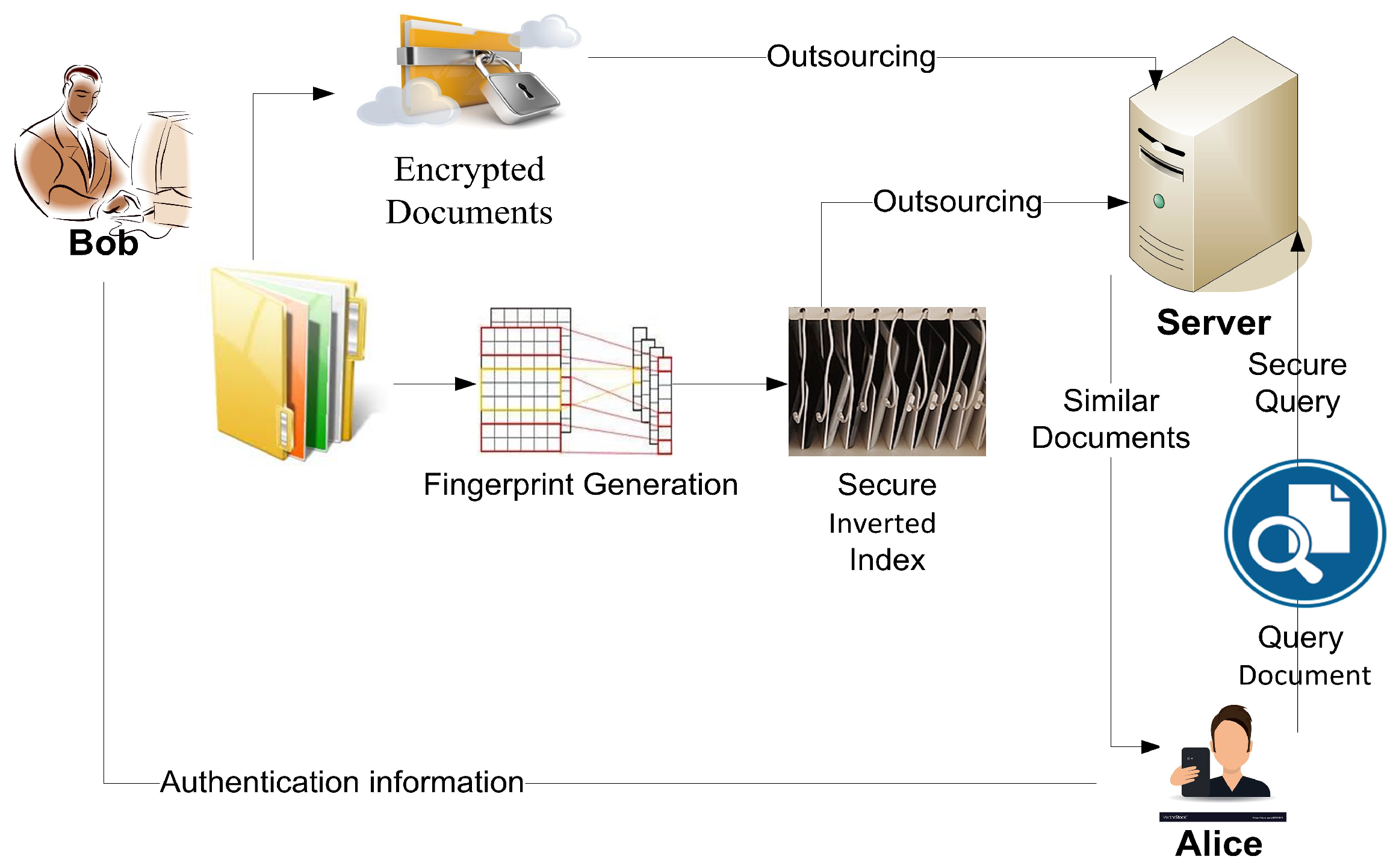
Applied Sciences | Free Full-Text | Lightweight, Secure, Similar-Document Retrieval over Encrypted Data | HTML

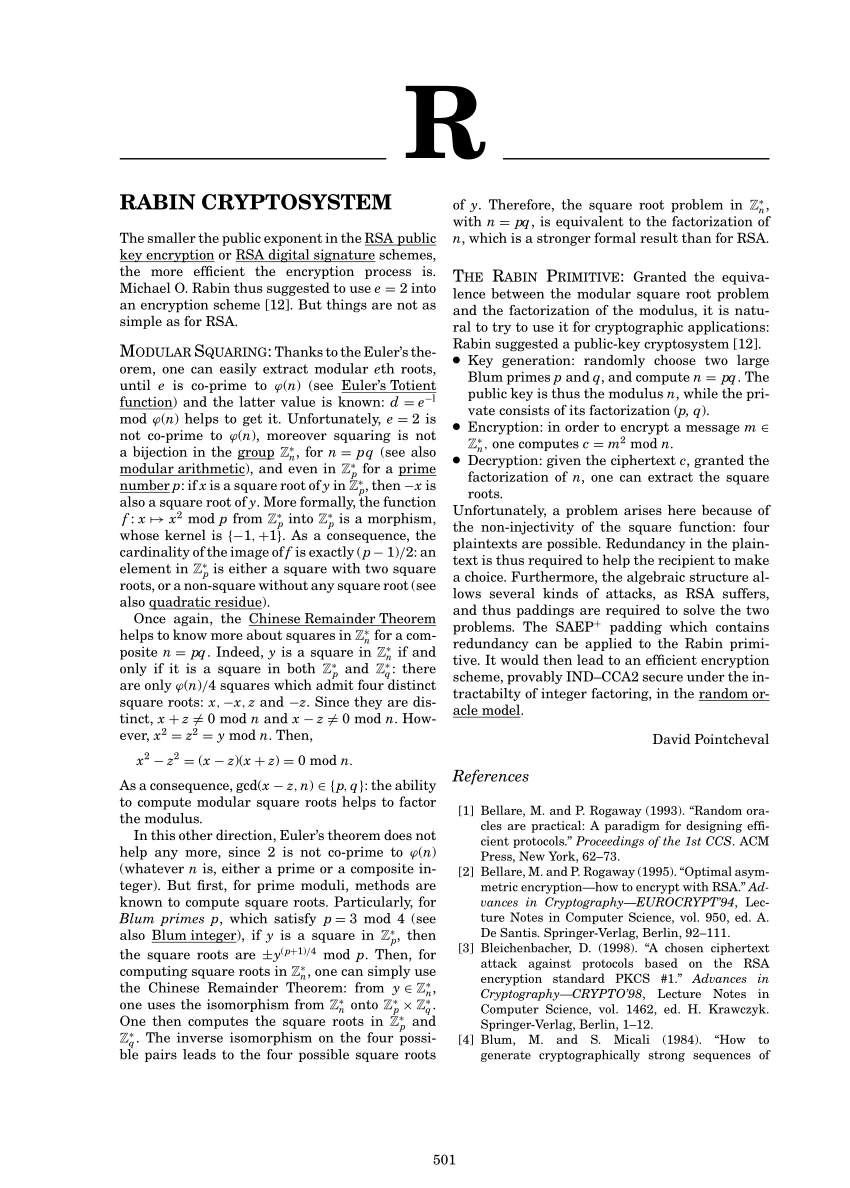
Wonk post: chosen ciphertext security in public-key encryption (Part 2) – A Few Thoughts on Cryptographic Engineering
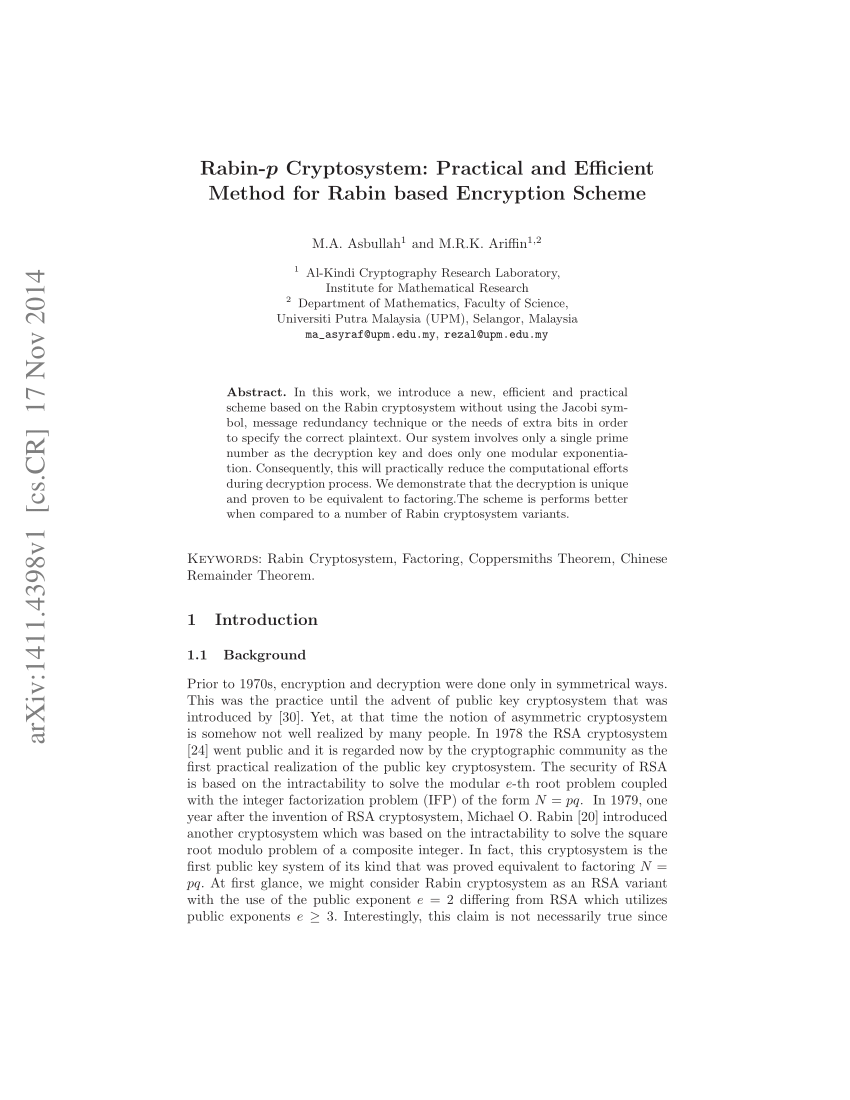
Rabin-p Key Encapsulation Mechanism A Proposal for Public Key Encryption for CyberSecurity Malaysia MySEAL Initiative

PDF) The Rabin Cryptosystem & analysis in measure of Chinese Reminder Theorem | ARPIT YUUVRAAJ Srivastava - Academia.edu



![PDF] Unique Rabin-Williams Signature Scheme Decryption | Semantic Scholar PDF] Unique Rabin-Williams Signature Scheme Decryption | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/dd75d50cae63bc00f6054781b5ac6990256e442d/14-Table1-1.png)

![PDF] Versatile padding schemes for joint signature and encryption | Semantic Scholar PDF] Versatile padding schemes for joint signature and encryption | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/0988eddbd5dc293ac23447de74c54e4d1c41267e/7-Figure3-1.png)
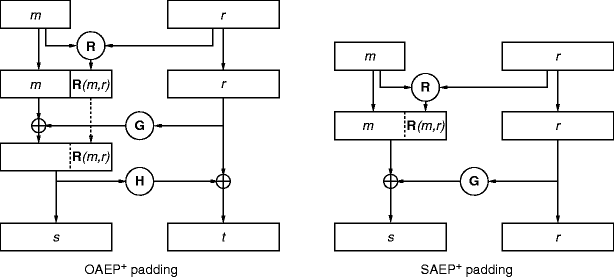
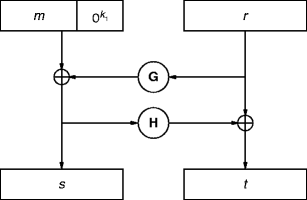

![PDF] Versatile padding schemes for joint signature and encryption | Semantic Scholar PDF] Versatile padding schemes for joint signature and encryption | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/0988eddbd5dc293ac23447de74c54e4d1c41267e/3-Figure1-1.png)